What Is VAPT?
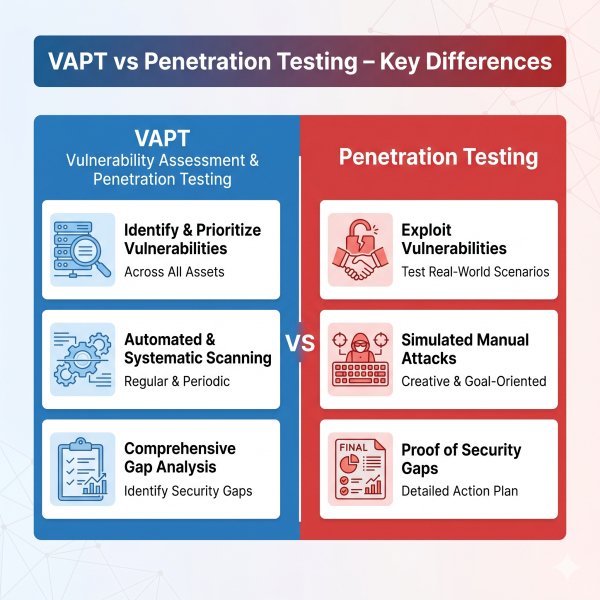
VAPT stands for Vulnerability Assessment and Penetration Testing.
It’s actually two things combined:
1. Vulnerability Assessment (VA)
- Think of this as a scan
- It finds weak points
- Example: outdated software, open ports, weak passwords
-
This is an attack simulation
-
It tries to exploit those weaknesses
So VAPT = Find problems + Try to break them
What Is Penetration Testing?
Penetration Testing (or pentesting) is just one part of VAPT.
It goes deeper. Instead of listing issues, it answers:
- Can a hacker actually break in?
- How far can they go?
- What damage can they cause?
It’s like hiring a legal hacker to test your system.
Types of VAPT Testing
Checks:
- Firewalls
- Servers
- Open ports
Checks:
- Login systems
- APIs
- Data leaks
Checks:
- Android & iOS apps
- Data storage issues
Checks:
- AWS, Azure misconfigurations
- Identity and access controls
Types of Penetration Testing
1. Black Box Testing
- No information given
- Simulates real hacker
2. White Box Testing
-
Full access given
-
Deep internal testing
3. Grey Box Testing
-
Partial access
-
Most practical approach
Real Risks You’re Ignoring Right Now
If you’re not doing proper testing:
- Your APIs are probably exposed
- Your employees are reusing passwords
- Your cloud permissions are misconfigured
- Your backups may not even work
And you won’t know until it’s too late.
When Should You Choose VAPT?
Use VAPT when:
You need compliance
You want broad visibility
-
Large infrastructure
-
Multiple assets (web, mobile, network)
You’re in early security maturity stage
You want periodic security hygiene checks
Reality check:
VAPT is your starting point, not your defense strategy.
When Should You Choose Penetration Testing?
Use penetration testing when:
You have a critical application
-
Banking app
-
SaaS platform
-
Payment gateway
You want to simulate real attacks
You need deep validation
-
Can attackers actually breach?
-
What data can they steal?
You’re launching a new product
You’ve already done vulnerability scans
Simple logic:
If a breach would cost you crores, pentesting is not optional.
Advantages and Limitations
VAPT Advantages:
-
Wide coverage
-
Cost-effective
-
Good for compliance
-
Identifies known vulnerabilities quickly
VAPT Limitations:
-
Limited depth
-
High false positives
-
Misses logic flaws
-
Doesn’t simulate real attackers fully
Penetration Testing Advantages:
-
Real-world attack simulation
-
Finds complex vulnerabilities
-
Shows business impact clearly
-
Reduces actual breach risk
Penetration Testing Limitations:
-
Narrow scope
-
Time-intensive
- Requires skilled testers
FAQs
1. Is VAPT mandatory for compliance?
Yes, most standards like ISO 27001, SOC 2, and PCI-DSS require vulnerability assessments. Some also expect penetration testing.
2. How often should VAPT be done?
At least once or twice a year. More frequently for dynamic environments.
3.. How often should penetration testing be done?
-
Before major releases
-
After significant changes
-
At least annually for critical systems
4. Is internal VAPT enough?
No. External perspective is critical. Internal teams miss blind spots.
5.What is included in a VAPT report?
Typically:
- List of vulnerabilities
- Severity ratings (CVSS)
- Basic remediation steps
Final Thoughts
If your company is growing, your risk is growing faster.Talk to digiALERT and understand your real risk before attackers do.
Contact now to schedule your FREE VAPT / Penetration Testing consultation - BOOK NOW