In the unending realm of cybersecurity, where innovation drives both defenders and adversaries, a distinct threat has arisen – the AirHopper attack. This sophisticated intrusion method challenges the very core of cybersecurity by bypassing conventional barriers and infiltrating isolated systems. In this extensive exploration, we embark on an illuminating journey into the complexities of the AirHopper attack, delving into its inner workings, potential impacts, and the arsenal of strategies available to counteract its covert incursions.
Decoding the AirHopper Attack: Penetrating the Impenetrable
Emergence of Aerial Espionage: Redefining Air-Gapped Infiltration
The AirHopper attack marks a watershed moment in cybersecurity, redefining the concept of air-gapped systems – those hermetically sealed from external networks. It leverages the manipulation of electromagnetic emissions, transforming them into an inconspicuous conduit for data exfiltration, thereby challenging the efficacy of traditional air-gap defense mechanisms.
Electromagnetic Emissions as Silent Couriers: A Covert Communication Channel
At the heart of the AirHopper attack lies the ingenious use of electromagnetic emissions. These emissions, which are typically discarded as innocuous byproducts of electronic activity, are harnessed as a silent means of communication. By repurposing these emissions, attackers create an unassuming pathway for covert data transmission that transcends the physical air-gap.
Stages of Intrusion Unveiled: Orchestrating a Subversive Symphony
- Implantation Phase: The assault commences with the surreptitious introduction of malicious code into the target system. A spectrum of entry points, including compromised USB drives and insider agents, serves as vectors for infiltration.
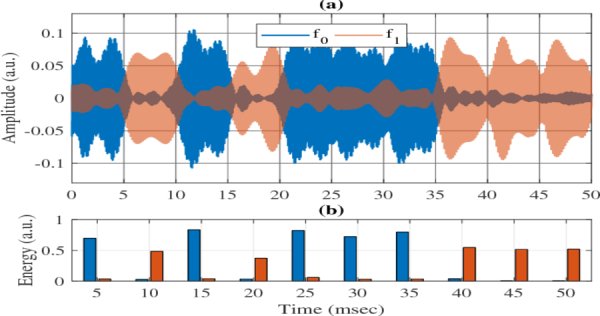
- Data Encoding Choreography: Extracted data undergoes intricate encoding to be compatible with electromagnetic signals. This transformation culminates in binary sequences, primed for their clandestine journey across the air-gap.
- Emission and Subjugation: As the compromised system operates, it inadvertently emits electromagnetic signals, concealing encrypted information. Armed with specialized hardware, the adversary captures and decrypts these signals from a distance.
- Decryption and Data Retrieval: The culmination of the attack involves decoding the intercepted signals, thus retrieving the original data. This process completes the exfiltration cycle without necessitating a traditional network connection.
Potential Ramifications of AirHopper: Breaching the Sanctity of Isolation
- Challenging Air-Gapped Integrity: An Era of Vulnerability
The AirHopper attack dismantles the aura of invulnerability associated with air-gapped systems. By exploiting this intrusion vector, the traditional insulation between isolated networks and the digital universe is compromised, redefining the parameters of cybersecurity.
- Espionage Amplified: Intellectual Property Pilferage
The reverberations of the AirHopper attack are profound. Threat actors can exploit this method for espionage, seizing sensitive data and intellectual property. The consequences ripple across economic realms, geopolitics, and the erosion of competitive advantages.
- Unmasking Potential Disruption: Critical Infrastructure Under Siege
In domains of critical infrastructure, an effective AirHopper assault could unleash chaos by infiltrating and manipulating air-gapped control systems. This dystopian scenario endangers essential services, casting a shadow over national security and public welfare.
Strategies to Subdue the AirHopper Threat: Forging Resilient Defenses
- Enforcing Physical Bastions: Bolstering Entry Points
Safeguarding physical access becomes pivotal. Rigorous access controls, vigilant surveillance, and periodic inspections counteract unauthorized implantation, bolstering the first line of defense.
- Cloaking Against Electromagnetic Emanations: Shielding Critical Components
Leveraging electromagnetic shielding methodologies dampens emissions from critical hardware components. By curtailing emissions, the potential for nefarious exploitation is drastically reduced.
- Architecting Network Fortifications: Segmentation as a Shield
While air-gapped networks hold value, network segmentation can curtail the impact of an AirHopper attack. Segregating critical systems from less sensitive ones contains lateral movement and mitigates potential breaches.
Examples and Evidence:
- Stuxnet Worm (2010): The Stuxnet worm, discovered in 2010, is a prime example of a sophisticated cyberattack that exploited air-gapped systems. Stuxnet was designed to target Iran's nuclear facilities, specifically its centrifuges. The worm employed multiple attack vectors, including USB drives, to breach the air-gap and manipulate the industrial control systems responsible for uranium enrichment. This incident highlighted the vulnerability of even highly secure air-gapped systems to targeted attacks.
- AirHopper Experiment (2014): Researchers from Ben-Gurion University in Israel conducted an experiment to validate the feasibility of the AirHopper attack. They successfully demonstrated how malware could be used to modulate electromagnetic emissions from a computer screen and transmit sensitive data to a nearby receiver using a software-defined radio. This experiment provided tangible evidence of how covert communication through electromagnetic emissions could breach air-gapped systems.
- Bridging the Air-Gap with LED Lights (2016): In a study conducted by researchers from the Cyber Security Research Center at Israel's Ben-Gurion University, a new variant of the AirHopper attack was demonstrated. This variant involved using the LEDs on a computer's hard drive to emit signals that could be intercepted by a nearby camera. By controlling the flickering of the LEDs, data could be encoded and transmitted, once again showcasing the creative ways in which air-gapped systems can be compromised.
- Eavesdropping through a Faraday Cage (2017): A team of researchers from the Cyber Security Group at the University of Electro-Communications in Japan demonstrated a variant of the AirHopper attack that utilized electromagnetic emissions even within a Faraday cage. By analyzing the unintentional electromagnetic radiation from computer components, they were able to reconstruct on-screen images from a computer located inside a Faraday cage. This experiment underscored the persistence of electromagnetic emissions and their potential for covert communication.
- Industrial Espionage in the Real World: While specific instances of the AirHopper attack might not be publicly disclosed due to their sensitive nature, real-world examples of industrial espionage underline the potential impact of such attacks. Organizations across industries, including manufacturing, energy, and defense, have fallen victim to cyberattacks that have compromised air-gapped systems, leading to data theft, intellectual property loss, and disruptions in operations.
Conclusion:
In the ever-evolving landscape of cybersecurity, where threats constantly mutate and breach barriers, the unveiling of the AirHopper attack serves as a stark reminder of the ingenuity of cyber adversaries. As we've delved into the intricate workings of this stealthy intrusion, one thing becomes abundantly clear – vigilance is the cornerstone of defense.
At DigiALERT, our mission is not just to inform, but to empower. The insights gained from understanding the AirHopper attack are invaluable, allowing us to craft innovative solutions that shield our clients from emerging threats. By collaborating with us, organizations can architect fortified digital landscapes, combining advanced technologies with vigilant practices.
The AirHopper attack is just one facet of the dynamic cyber world. As we navigate this intricate landscape together, DigiALERT stands as your partner, arming you with the tools to anticipate, detect, and thwart threats that seek to breach your defenses. Together, we illuminate the depths of cyber intrusion, fortifying your digital realm against the relentless tides of innovation-driven challenges.